Update: Microsoft acknowledged PrintNightmare as a zero-day that has been affecting all Windows versions since before June 2021 security updates.
Technical details and a proof-of-concept (PoC) exploit have been accidentally leaked for a currently unpatched vulnerability in Windows that allows remote code execution.
Despite the need for authentication, the severity of the issue is critical as threat actors can use it to take over a Windows domain server to easily deploy malware across a company’s network.
The issue affects Windows Print Spooler and because of the long list of bugs impacting this component over the years [1, 2, 3, 4], the researchers named it PrintNightmare.
Several researchers have tested the leaked PoC exploit on fully patched Windows Server 2019 systems and were able to execute code as SYSTEM.
An accidental leak
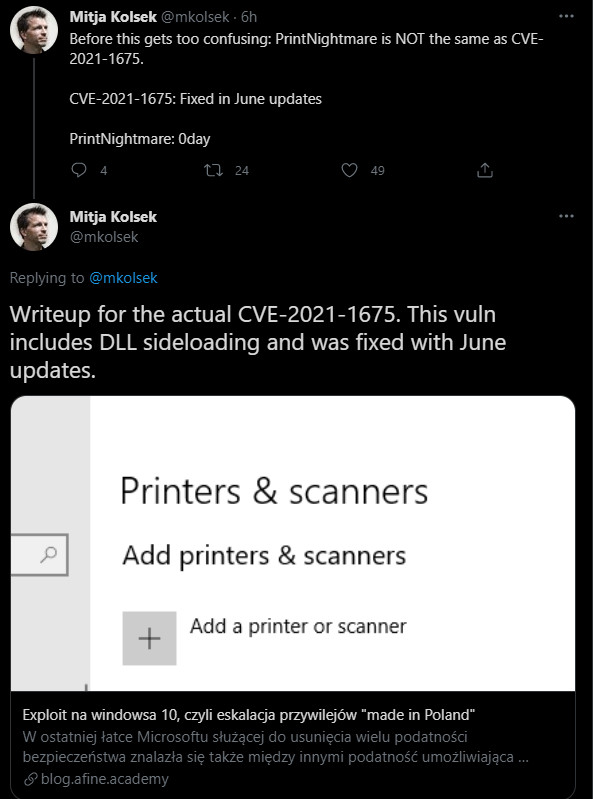
Leaking the details for this vulnerability happened by accident, out of a confusion with another issue, CVE-2021-1675, also impacting Print Spooler that Microsoft patched in this month’s rollout of security updates.
Initially, Microsoft classified CVE-2021-1675 as a high-severity, privilege escalation issue but a couple of weeks later changed the rating to critical and the impact to remote code execution, without providing any details.
Credited for reporting CVE-2021-1675 are researchers from three cybersecurity companies (Tencent, AFINE, NSFOCUS) but multiple teams were analyzing Windows Print Spooler.
On June 28, Chinese security vendor QiAnXin announced that they found a way to exploit the vulnerability to achieve both local privilege escalation and remote code execution, and published a demo video.
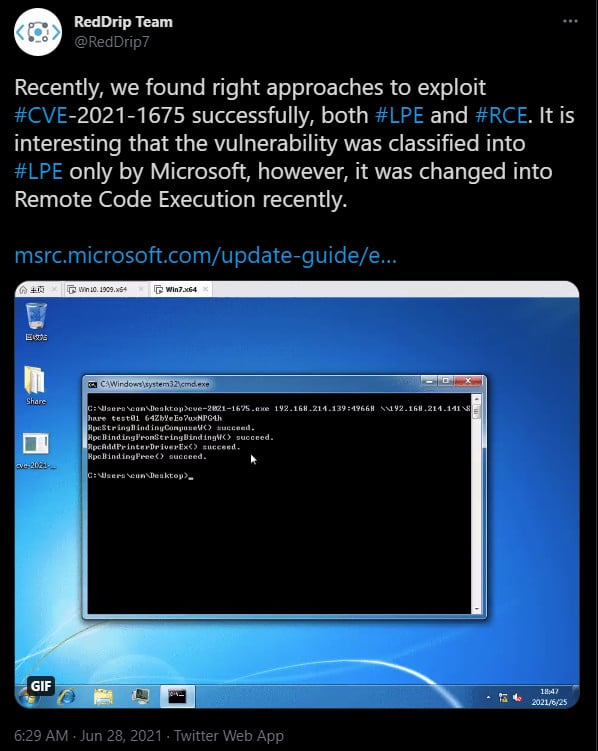
Seeing the exploit video, another team of researchers from Chinese security company Sangfor, decided to release their technical writeup and a demo exploit for remote code execution (RCE), calling the bug PrintNightmare.
It turns out that Microsoft's patch for CVE-2021-1675 on June 8 was incomplete and the PrintNightmare RCE exploit works on up-to-date systems.
With no information from Microsoft about the issue, the vulnerability created confusion among security researchers, some of them believing that PrintNightmare was a separate, zero-day flaw that needed its own identification. [see Update 3]
Mitja Kolsek, CEO of Acros Security and co-founder of micropatching service 0Patch tried to clear the confusion by pointing to the technical details that AFINE researchers released for CVE-2021-1675.
Nevertheless, one of the researchers that reported CVE-2021-1675 to Microsoft, Yunhai Zhang of NSFOCUS, offered an explanation about why the patch does not stop the PrintNightmare exploit.
"CVE-2021-1675 is meant to fix PrintNightmare, but it seems that they just test with the test case in my report, which is more elegant and also more restricted. So, the patch is incomplete. : ( " - Yunhai Zhang
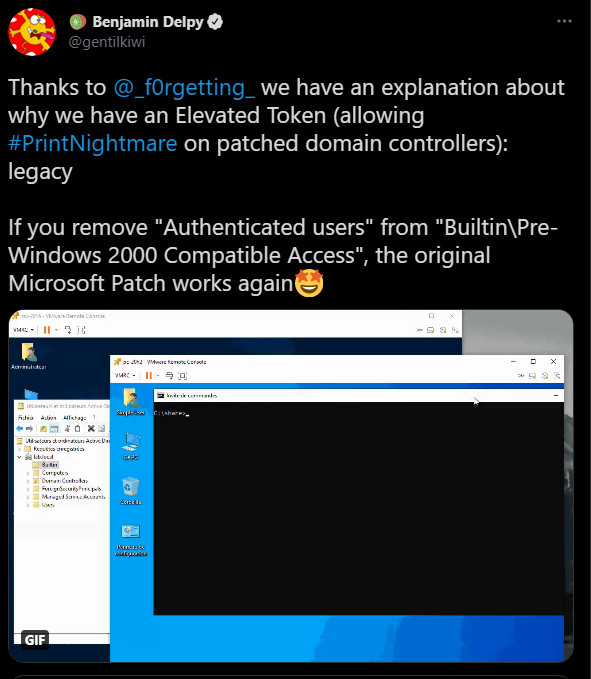
Benjamin Delpy, the developer of mimikatz post-exploitation tool for penetration testing, clarified things even more by noting that only patched servers promoted to domain controllers are affected.
Confusion aside, PrintNightmare is a serious flaw that needs to be treated accordingly.
Since a patch is yet to come, administrators are strongly advised to stop and disable the spooler service on domain controller systems.
Security consulting company Lares published a repository with detection and remediation information that includes a sample of the PrintNightmare attack and a Sysmon configuration file for telemetry purposes.
Florian Roth of Nextron Systems created experimental Sigma rules for detecting print spooler exploitation based on Sangfor researchers' exploit code.
Lares also provides details on how to stop and disable the spooler service either from the Group Policy settings or by using a PowerShell script. CERT/CC has also released instructions on how to stop and disable the Print Spooler service.
Matthew Hickey, co-founder of Hacker House, was able to obtain full SYSTEM privileges from a normal Domain User account on an up-to-date Windows Server 2019 machine vulnerable to PrintNightmare.
Delpy achieved remote code execution with the highest privileges on a fully patched system, too. While his test was also on a Domain Controller, Delpy said that the same result is achieved “on all systems with RPC to spooler available, remote or local.”
Delpy made a video showing that his test system, running the latest updates, did not stop the PrintNightmare exploit:
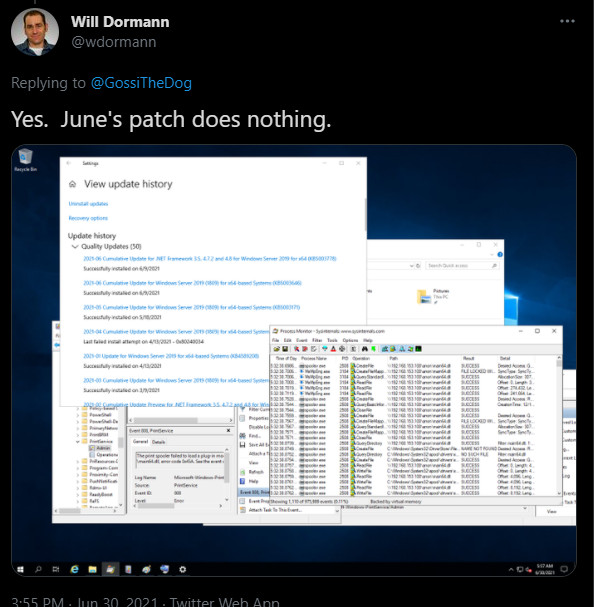
Will Dormann, a vulnerability analyst for CERT/CC confirmed that a remote, authenticated attacker can run code with elevated rights on a machine with the Print Spooler service enabled.
Dormann also confirmed that Microsoft’s June security updates have no effect against the PrintNightmare zero-day vulnerability detailed by the researchers from Sangfor.
The general advice at the moment is to stop and disable the service on Domain Controllers as soon as possible, as the need for authentication is far from a deterrent for an attacker.
Threat actors, ransomware groups in particular, are likely to jump at the occasion to compromise company networks, since getting credentials for limited-privilege domain users is an easy task, security researcher Jonas Lykkegård told BleepingComputer.
Credentials for regular users can be just as good for an attacker in environments vulnerable to privilege escalation, and there is a market for this type of data, sustained by info-stealing activities.
On some underground forums, a valid login and password pair for a Windows Remote Desktop server can go for as low as $3 and as high as $70.
One of the largest marketplaces for Windows Remote Desktop logins had a collection of 1.3 million credentials, showing that selling them is a lucrative business.
Sangfor researchers (Zhiniang Peng, XueFeng Li, and Lewis Lee) will talk at Black Hat this year about how they found PrintNightmare and created an exploit for it in a presentation titled Diving Into Spooler: Discovering LPE and RCE Vulnerabilities in Windows Printer.
Update [June 30, 18:45 EST]: Added information about detecting PrintNightmare exploit attempts and disabling the print spooler service to prevent attacks.
Update [July 1]: Added comment on PrintNightmare being the same as CVE-2021-1675 from Yunhai Zhang of NSFOCUS, credited for the discovery and reporting of the vulnerability, and from penetration tools developer Benjamin Delpy.
Update [July 2]: Microsoft has provided the much needed clarification on PrintNightmare by saying that it is "similar but distinct from the vulnerability that is assigned CVE-2021-1675" and that it existed before the June 2021 security updates.
PrintNightmare exists in all versions of Windows and it was assigned a new identification number, CVE-2021-34527. Microsoft warned its Microsoft 365 Defender customers that the vulnerability is actively exploited by attackers.


Comments
neutroncore - 2 years ago
Your missing the : in the source link under the image :)